Why is an approval needed?
Using our app requires delegated access to Microsoft 365, via the Microsoft Graph API. We use the most common form of delegated authentication flow, the authentication code flow via an Enterprise application. In many cases, access to Microsoft Graph resources is restricted by default. If you can’t login from Jira or Microsoft Teams, your Microsoft 365 or Azure administrator might need to consent to the app for you.
In case you are interested in the exact permissions and why we need them, please check out this dedicated permissions article.
Technical ids & scopes
Below you can find a list of necessary client ids and scopes. You only need to allow the Enterprise apps in case the feature should be used. Depending on the feature, there are also optional scopes which enhance the basic functionality, but are considered optional by us and can be omitted if not required - the app will gracefully handle the missing scopes.
The following base scopes are required for all features:
email
offline_access
profile
openid
|
App feature |
Enterprise app client id |
Scopes |
|---|---|---|
|
|
|
|
|
Meetings |
|
optional Necessary for certain features to work, e.g. searching for rooms |
|
Bookings |
|
|
|
Calendar |
|
optional Necessary for certain features to work, e.g. searching for rooms & embedding Teams channel calendars |
|
To Do |
|
|
|
Teams |
|
optional The Smart Connect bot keeps chats shared - independently of participants leaving the chat or company. |
|
Teams JSM portal |
|
|
|
Teams JSM portal notifications |
|
Since the portal link is an individual link we can’t provide a direct link to approve for all users. Feel free to see our docs to get the direct link: Approve for all users |
Approving access for all users for our apps
To approve access for all users for the relevant apps, please send your Office 365 administrator the following links or use the links above. In this case your admin has to approve for every app separately.
|
App feature |
Approval link |
|
|---|---|---|
|
Email, Calendar, Meetings (incl. optional scopes) |
|
|
|
|
|
|
|
Meetings |
With room support
|
|
|
Calendar |
Only mandatory scopes:
With Teams channel calendar, group & room support
|
|
|
To Do |
|
|
|
Teams |
|
|
|
Teams JSM portal |
|
|
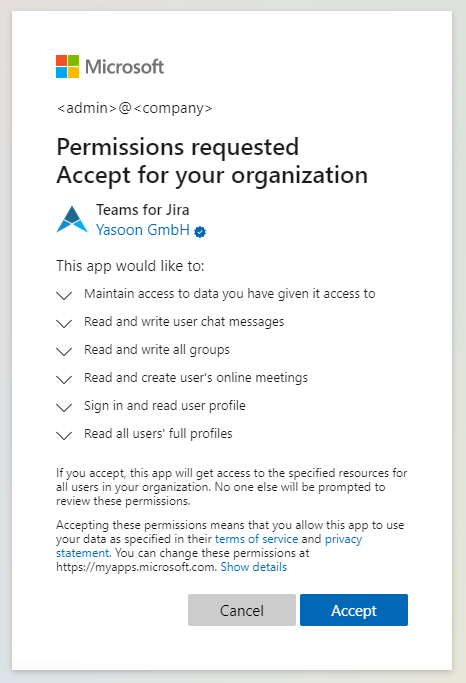
Your admin will see the following screen, where the permissions can be confirmed.
Please note, that despite what the screen says in the subtext, we won’t get access to all user resources automatically after approving this. Before we can get access to any Office data, the users will need to log in with their own account as well from Jira.
Approving access for a limited set of users
Using Entra ID configurations
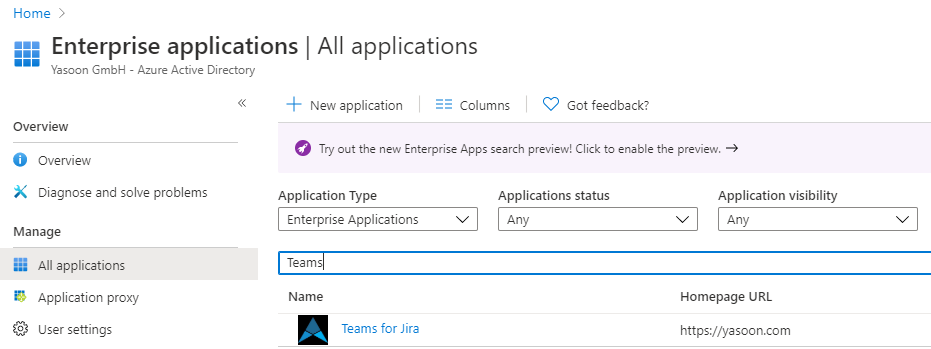
Please go to https://entra.microsoft.com/ → Applications → Enterprise applications and search for our apps.
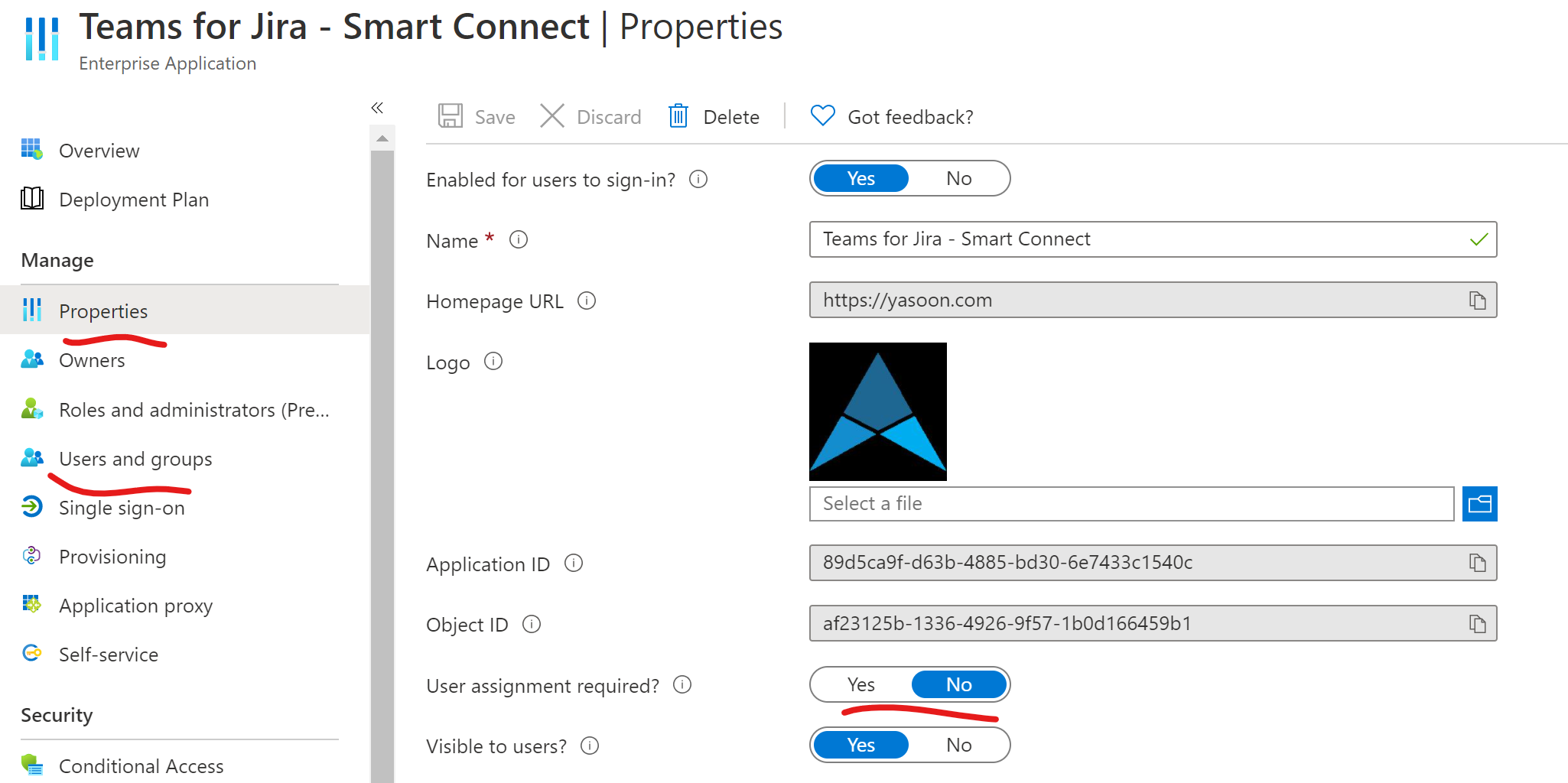
There are basically three steps to allow the app only for certain users:
-
Make assignment of the app required. This way only assigned users will be able to login in the first place.
-
Assign the relevant users to the app
-
Grant admin consent for the app for the organization
→ Only the assigned users can login and don’t need to ask for approval:
Using Powershell
In case you only want to approve the access for a limited set of users, e.g. you already have a dedicated AzureAD group for Jira users, you’ll need to do this via a Powershell script. The easiest way is to create a new .ps1 file on your computer and paste the following code. Make sure to adjust the client ids and scopes according to the table above.
# Install Microsoft Graph Powershell toolkit
Install-Module Microsoft.Graph -Scope CurrentUser
# The app for which consent is being granted. In this example, we're granting access
# to the Microsoft Teams Jira feature, use one of the following:
# -----------------------------------------------------------------
# Email e7185a25-9df9-4d05-b779-76b04bf46424
# Meetings e7185a25-9df9-4d05-b779-76b04bf46424
# Calendar e7185a25-9df9-4d05-b779-76b04bf46424
# To Do 32d752a1-8945-4600-97c9-73ed32c3627a
# Teams 89d5ca9f-d63b-4885-bd30-6e7433c1540c
# Teams JSM portal a47ed889-74d6-4acf-b5c8-b1172696eb70
$clientAppId = "89d5ca9f-d63b-4885-bd30-6e7433c1540c" # Teams
# The permissions to grant. Here we're including "openid", "profile", "User.Read"
# and "offline_access", "email" (for basic sign-in), as well as feature specific scopes
# Email @("openid", "profile", "offline_access", "User.Read", "email", "Mail.ReadWrite.Shared", "Mail.Send.Shared", "People.Read", "User.ReadBasic.All")
# Meetings @("openid", "profile", "offline_access", "User.Read", "email", "Calendars.ReadWrite.Shared", "OnlineMeetings.ReadWrite", "User.ReadBasic.All")
# Calendar @("openid", "profile", "offline_access", "User.Read", "email", "Calendars.ReadWrite", "Calendars.ReadWrite.Shared", "OnlineMeetings.ReadWrite", "People.Read", "User.ReadBasic.All", "Place.Read.All", "Group.ReadWrite.All", "Team.ReadBasic.All")
# To Do @("openid", "profile", "offline_access", "User.Read", "email", "Tasks.Read", "Tasks.ReadWrite", "Tasks.ReadWrite.Shared")
# Teams @("openid", "profile", "offline_access", "User.Read", "email", "Channel.ReadBasic.All", "ChannelMessage.Send", "Chat.ReadWrite", "Team.ReadBasic.All", "User.ReadBasic.All")
# Teams JSM portal @("openid", "profile", "offline_access", "User.Read", "email")
# For Teams
$permissions = @("openid", "profile", "offline_access", "User.Read", "email", "Channel.ReadBasic.All", "ChannelMessage.Send", "Chat.ReadWrite", "Team.ReadBasic.All", "User.ReadBasic.All")
# Step 0. Connect to Microsoft Graph PowerShell. We need User.ReadBasic.All to get
# users' IDs, Application.ReadWrite.All to list and create service principals,
# DelegatedPermissionGrant.ReadWrite.All to create delegated permission grants,
# and AppRoleAssignment.ReadWrite.All to assign an app role.
# Group.Read.All is necessary if you want to use users from a security group
Connect-MgGraph -Scopes ("User.ReadBasic.All Application.ReadWrite.All " `
+ "DelegatedPermissionGrant.ReadWrite.All " `
+ "AppRoleAssignment.ReadWrite.All " `
+ "Group.Read.All")
# Step 1. Check if a service principal exists for the client application.
# If one does not exist, create it.
$clientSp = Get-MgServicePrincipal -Filter "appId eq '$($clientAppId)'"
if (-not $clientSp) {
$clientSp = New-MgServicePrincipal -AppId $clientAppId
}
Write-Host "Service principal for $($clientAppId) is $($clientSp.Id)"
# Step 2. Define users that should have the app consented
# Either use a single, hard coded user (upn or GUID)
$userIds = @((Get-MgUser -UserId "someuser@contoso.com").Id)
# Or assign app based on a security group
# $userIds = Get-MgGroupMember -GroupId '<groupGuid>' -All | % {$_.Id }
# Loop over selected users
foreach ($userId in $userIds)
{
# Step 3. Create a delegated permission that grants the client app access to the
# API, on behalf of the user. If the existing grant already exist, skip creating it
# Note: In case of changed scopes, this is not updated automatically yet
$existingGrant = Get-MgOauth2PermissionGrant -Filter "consentType eq 'Principal' and principalId eq '$($userId)' and clientId eq '$($clientSp.Id)'"
if (-not $existingGrant) {
$resourceSp = Get-MgServicePrincipal -Filter "appId eq '00000003-0000-0000-c000-000000000000'"
$scopeToGrant = $permissions -join " "
New-MgOauth2PermissionGrant -ResourceId $resourceSp.Id `
-Scope $scopeToGrant `
-ClientId $clientSp.Id `
-ConsentType "Principal" `
-PrincipalId $userId
# Step 4. Assign the app to the user. This ensures that the user can sign in if assignment
# is required, and ensures that the app shows up under the user's My Apps.
# The app role ID 00000000-0000-0000-0000-000000000000 is the default app role
# indicating that the app is assigned to the user, but not for any specific
# app role.
New-MgServicePrincipalAppRoleAssignedTo `
-ServicePrincipalId $clientSp.Id `
-ResourceId $clientSp.Id `
-PrincipalId $userId `
-AppRoleId "00000000-0000-0000-0000-000000000000"
}
}
Creating the Enterprise application only for review purposes
In case you want to inspect the app first before approving is, you can just add the service principal to AzureAD.
Do do this, you’ll need to use Powershell to create it manually. For the “AppId” parameter, use one of the client ids listed in the table above, in this case the one for Teams.
# Install Powershell module for Azure (if you don't have it yet)
Install-Module AzureAD
# Connect to Azure interactively
Connect-AzureAD -Confirm
# Create the new service principal
New-AzureADServicePrincipal -AppId 89d5ca9f-d63b-4885-bd30-6e7433c1540c -Tags {WindowsAzureActiveDirectoryIntegratedApp}
Afterwards, you should be able to find the enterprise app in the UI linked above, where you can restrict the application to certain users or groups, or, using the “Properties” page, allow users to self-approve the app:
References
https://docs.microsoft.com/en-us/azure/active-directory/manage-apps/configure-admin-consent-workflow
https://docs.microsoft.com/en-us/azure/active-directory/manage-apps/grant-admin-consent
https://docs.microsoft.com/en-us/azure/active-directory/manage-apps/grant-admin-consent
